The Zyxel USG Flex 100 is the entry-level security firewall gateway from the new USG Flex series and yes, it does have pretty much all the features of the older USG series, but Zyxel now relies a lot more on the Cloud Query service (that it has unveiled last year) to help deliver a better UTM firewall performance, while requiring less resources from the device itself. This way, there is a far higher detection rate for possible threats (while in the past it would have gone beyond the hardware capacity).
Of course, the internal hardware has been improved (to meet the exigence of 2020) and yes, the SSL, IPsec and L2TP-based VPNs are still there (as well as the large amount of customization), but why call it FLEX?
It’s an acronym for Flexible and it refers to the subscription plans which are more flexible: the user can either choose single license configurations or migrate unexpired ones from older USG devices.

Besides the Zyxel USG Flex 100, the manufacturer has also made available the Flex 200 and Flex 500 which are a bit more faster and have a higher variety of ports – while the rest of the devices from the series have more than one WAN port, the Flex 100 seems to be the only member to come with a single WAN port (it does have an SFP port and support for 3G/4G modems, as well as the OPT port, all with the potential of functioning as an additional WAN interface).
IMPORTANT: It was found that the USG series running the ZLD v4.60 is vulnerable to third-party attacks (a backdoor account was discovered), so you should immediately update the device to get the latest patch that fixes this vulnerability.
Design and Build Quality
If you’re familiar with Zyxel USG40 (or the newer NSG50), the USG Flex 100 has pretty much the same design and it’s no surprise since the USG Flex 100 is also known as USG40v2. The gateway features a metallic gray box with a plastic front and with a couple of red accents on the left and right side which are characteristic to the series. Furthermore, the device is very compact (it measures 11.18 x 7.48 x 3.94 inches) and no, you won’t be able to mount it in a rack since there are no holes on the sides to allow you to attach any extensions (if you must put it in a rack, there is the tray option). Inside the package, there are four rubber feet which need to be glued to the bottom of the Flex 100 if you intend to leave it on a desk, otherwise, there are two dedicated holes on the bottom to mount the device on the wall.
Another similarity with the Zyxel USG20-VPN is that this gateway is fanless (the original USG20 did have a fan), so it fully relies on passive cooling. At the moment, there are about 86 degrees F outside (approx 80 inside) and I noticed that the Zyxel USG Flex 100 did get a bit warm on the top and hot on the bottom which means that those feet are mandatory to allow some airflow underneath the case; despite running a bit hot, there were no signs of throttling or overheating – it’s worth mentioning that Zyxel has added lots of cut-outs on the top of the device, as well as on the sides to keep the internal temperature low. In terms of power consumption, since this is the entry-level model, it is also the most efficient, requiring no more than 7 watts (on average) and at full load, it can go up to 12.5 W (which is still quite low for a networking device of its caliber).

On the front of the device, next to the red plastic piece with the name and number, there’s a recessed Reset button (press and hold it for about 5 seconds until the SYS LED starts blinking to return the device to its default settings), followed by two LEDs: PWR (if it gets red, then there’s a hardware failure) and SYS (flashes green when the gateway is booting). Further to the right, there are six LEDs, from P1 to P6 (WAN/LANN/DMZ) and these LEDs are going to be yellow when the connection is made at 1000Mbps or green, when the connection is made at 10/100 Mbps. Lastly, there’s a USB 3.0 port which can be useful for connecting external storage devices or 3G/4G USB modems (for WAN failover).
On the rear side of the Zyxel Flex 100, there is a 12V Power connector, an ON/Off button, a Gigabit SFP P1 port (suitable for a fiber connection), a Console port (this port can be used to manage the device via CLI commands – Zyxel has added a Console cable inside the package and be aware that the host computer does need to have a communication software configured in a certain way – check the official user guide at page 71), a WAN P2 port (for the main Internet connection) and four other LAN/DMZ ports (P3 to P6).
| Zyxel USG Flex 100 | Zyxel USG Flex 200 | Zyxel USG Flex 500 | |
| LAN Ports | 4 | 4 | 7 |
| WAN Ports | 1 | 2 | Configurable |
| SFP Ports | 1 | 1 | 1 |
| USB Ports | 1 | 2 | 2 |
| Console Ports | 1(RJ-45) | 1(DB9) | 1(DB9) |
| Firewall Throughput (Mbps) | 900 | 1,800 | 2,300 |
| VPN Throughput (Mbps) | 270 | 450 | 810 |
| IDP Throughput (Mbps) | 540 | 1,100 | 1,150 |
| Max. IPsec VPN tunnels | 40 | 100 | 300 |
| Max. SSL VPN users | 30 | 60 | 150 |
Hardware
To have a look at the internal hardware of the Zyxel USG Flex 100, I removed all the six screws (be aware that there’s one hidden underneath the sticker with the Zyxel logo) and, after removing the small aluminum cover, I saw that Zyxel still favors Cavium, so the USG Flex 100 is equipped with a dual-core Cavium Octeon III CN7020-1200WG640-AAP-G chip (clocked at 1.2GHz) and four Nanya 1922 NT5CC512M8EN-EK (amounting to 2GB DDR3).
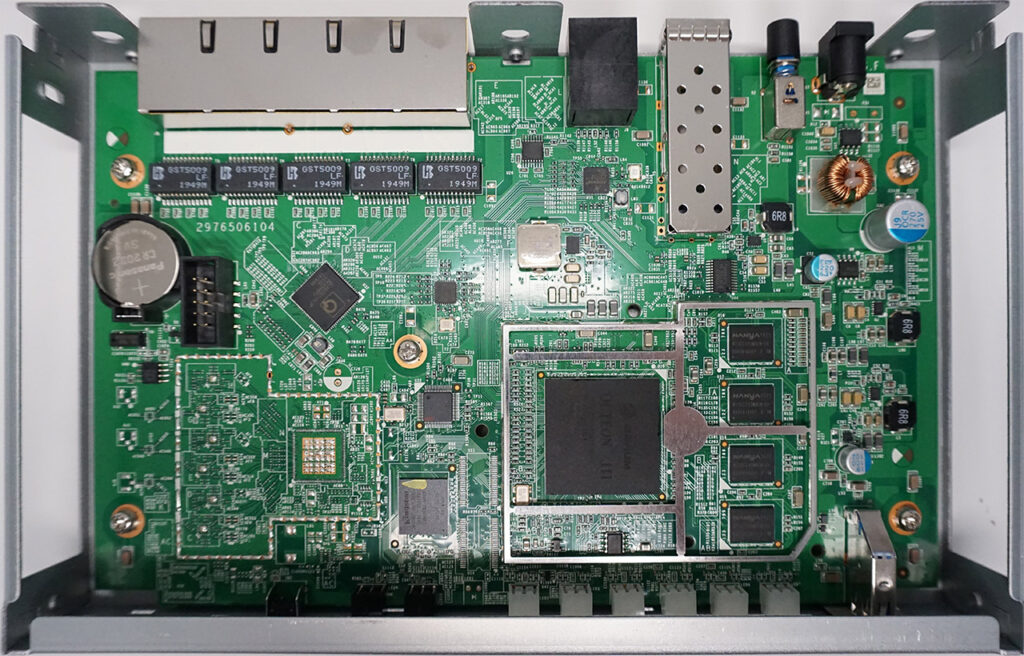
Furthermore, I could also identify a QCA8337 AL3C PK9398R3 Ethernet switch, a Qualcomm Atheros AR8033 AL1A NJ941229 PHY 3-CH 10Mbps/100Mbps/1Gbps, 8GB of flash memory from Kingston (EMMCC08G-M325), an Intel ALTERA 5M160ZE64C5N CPLD, a SIPEX 3232EC 1913L HCW8J transceiver, four GST5009 LF 1949M 1000 Base-T Magnetics Modules and a NXP PCA9555 24-pin CMOS device. As you can see, there are no WiFi chips or antennas and that’s because this firewall gateway doesn’t support WiFi.
The entire Flex series lacks a model with WiFi (some other USGs did come with external antennas – the models that would end with W) so, to connect your wireless clients, you will have to rely on some wireless access points.

As a side note, the Zyxel USG Flex 100 was designed to seamlessly integrate with some Unified and Unified Pro models, such as the NWA5123-AC HD. What you gain by sticking with Zyxel APs is central management, data forwarding, auto provisioning and yes, there’s also support for ZyMesh.
Zyxel USG Flex 100: Installation and Configuration
The installation process is very straight forward and it’s very similar to the one on consumer-grade routers: connect the WAN port to the modem, the Power cable and turn the device on and lastly, use an Ethernet cable to connect the firewall gateway to a computer; you can also add any wireless access point since the wizard will allow you to make a quick WiFi configuration. After the USG Flex 100 is connected to a computer, enter 192.168.1.1 in the browser and insert admin/1234 for the username and password. You will then be prompted to change the password and you can start the Quick Activation Wizard. On the first step, you can configure the First WAN interface (this model does not have the Second WAN interface config available in the Wizard), which, in my case, it was PPPoE, followed by the Date and Time set up and the Firmware Upgrade.
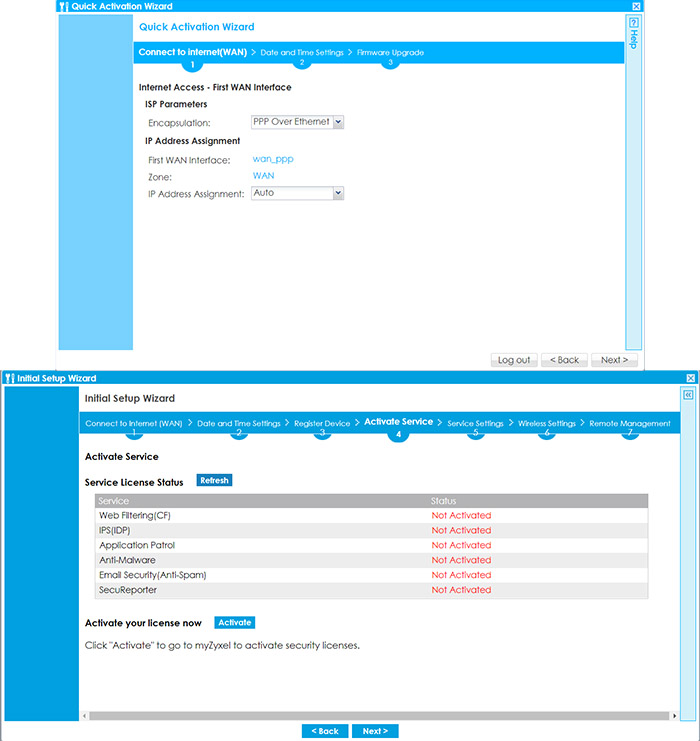
From here on, you can register the device and, if you already have an account, it’s going to be a matter of two clicks and you don’t have to enter any data since the process is automatic. After the product has been registered, you will arrive at the Activate Service window; here, there are the available Service License Status where there’s the option to quickly activate your license (again, with only a couple of clicks). If you decide to do it later, it can be easily done by visiting http://portal.myzyxel.com, entering your credentials and then manage your registered devices, the licenses and there’s also the option to download the latest firmware. Returning to the Wizard, the next page is the Service Settings, where you can Enable or Disable various services (such as URL Threat Filter, the Anti-Malware, IDP, Content Filter, App Patrol, Email Security and SecuReporter). You can also quickly set up the Wireless Settings (if you have a wireless access point available) and enable the Remote Management.
After that’s done, you can now roam the interface and there are a few elements that immediately stand out. The first one is the Virtual Device section, where you get to see an accurate graphical representation of both the front and the rear side of the device, then, there are various boxes containing different sets of status info, such as the Device Information (you can also update the firmware here), the System Status, CPU, Memory and Flash Usage and more.
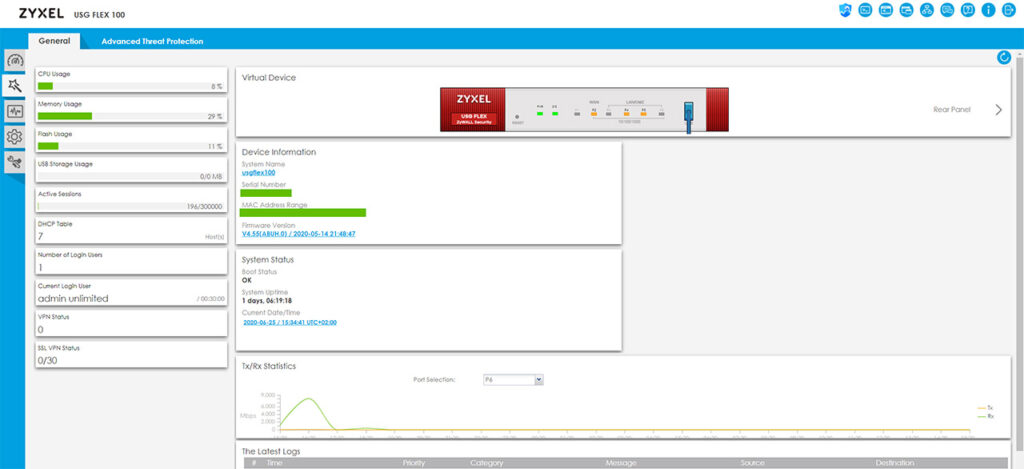
Next to the General section, there’s also the Advanced Threat Protection section, where you get to see the security features in action (the number of scanned files, the number of threats found and more). Before moving on, it’s worth mentioning that on the top right side, there is an area where you can visit the SecuReporter (it’s a completely separate interface on the Zyxel servers). There’s also the possibility to use the Web Console and CLI, to check the Site Map and Logout.
Dual-WAN and Load Balancing
The Zyxel USG Flex 100 has a single default WAN port (that you can configure in the Wizard), but you can also set up a secondary Internet connection by clicking on the Quick Setup, selecting the WAN Interface and then choosing between the three available options: SFP, WAN or OPT. For this application, I selected the OPT port and since I had a secondary PPPoE connection that I borrowed from a neighbor, the setup process is going to be similar to the first WAN connection. To view the Ports and do any further adjustment, go to Configuration > Network > Interface.
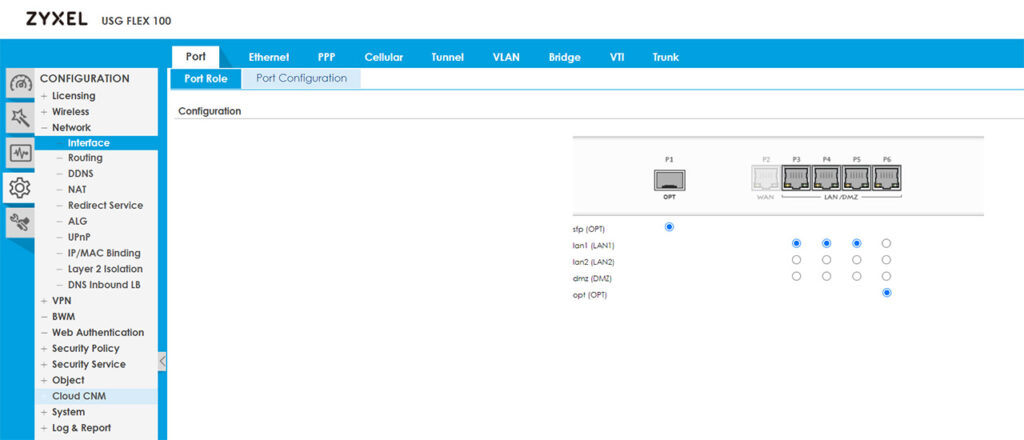
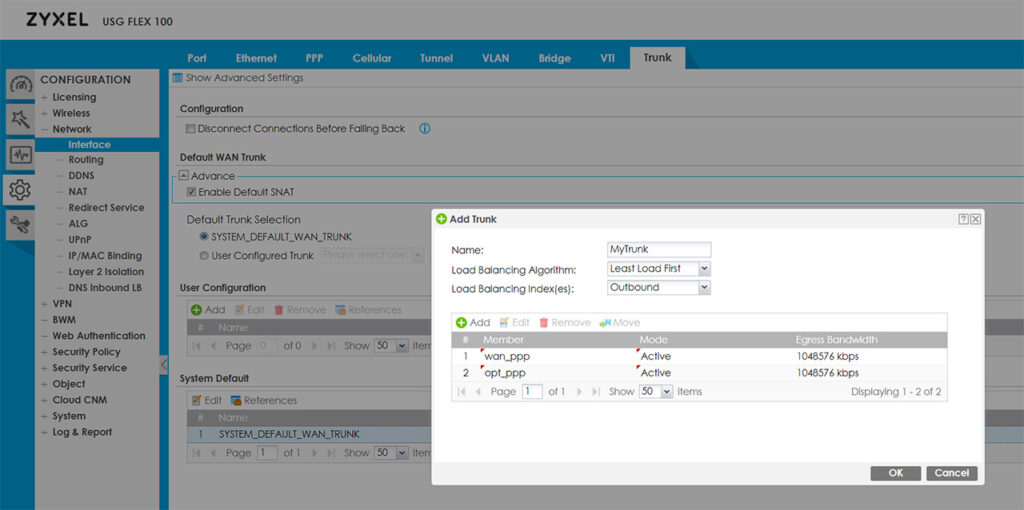
If you have more than one ISP connection and want to balance the traffic load for a better bandwidth utilization, you will have to use trunks (Network > Interface > Trunk). Without doing any changes to the previous configuration and simply disconnecting any of the two links, I saw that the router would automatically switch to the active links and that’s because the USG Flex 100 uses the System Default WAN Trunk, which, in turn uses the Least Load First algorithm. This algorithm decides which interface should be used for the traffic by checking the outbound bandwidth utilization of each member interface (there is also the option to use the inbound traffic from the LAN or both the inbound and the outbound traffic).
Another important aspect is that you can decide the Mode for each trunk interface, so it can either be Passive or Active and if you look towards the top of the page, you will see that under Configuration, you can enable the ‘Disconnect Connections Before Falling Back’, which means that when an Active connection regains the link, the passive ones get automatically disconnected. Besides the Least Load First, there is also the Weighted Round Robin algorithm which is best used when the bandwidth set for each WAN interface is different and the way it works is by distributing client requests to servers, each taking turns on a rotating basis. Furthermore, each interface gets assigned a weight and based on this weight, a server may handle one or more sessions.
Lastly, there’s the Spillover algorithm which sends the traffic to the first WAN interface and, when the maximum allowed load is reached, the traffic in excess is then sent to the next interface from the trunk list. If you only want to configure FailOver from the first WAN to the second and don’t want to use Trunk, you will need to go to Routing > Policy Route and set the Incoming Interface to the first WAN and the Next-Hop as the secondary and create a new Policy Route the other way around (don’t forget to Enable the Connectivity Check). I noticed that when I disconnect the Internet from the first WAN interface, it takes about 5 seconds for the second link to become active – it took about the same time the other way around.
VPN
The Zyxel USG Flex 100 supports IPSec, SSL and L2TP VPN and I do like that the manufacturer has added Configuration Walkthroughs to help with setting up each one of them (quite useful with devices such as the USG firewalls, where you get to set every parameter, but it’s easy to get lost in the myriad of options). To set up the IPSec VPN, you can use the VPN Setup Wizard (the second option on the left) and follow the steps to create a new VPN Provisioning Rule; afterwards, go to Configuration > Object < Add a User and create a new IPSec VPN Client. Next, go to the Configuration > VPN > IPSec VPN > Configuration Provisioning and pair the VPN Connection to the newly create Allowed User. Afterwards, you will have to download the ZyWall IPSec VPN Client (there is a direct link from the interface – be aware that it’s license based, but you can use the trial version for 30 days) and insert the default gateway, as well as the user that you previously set up.
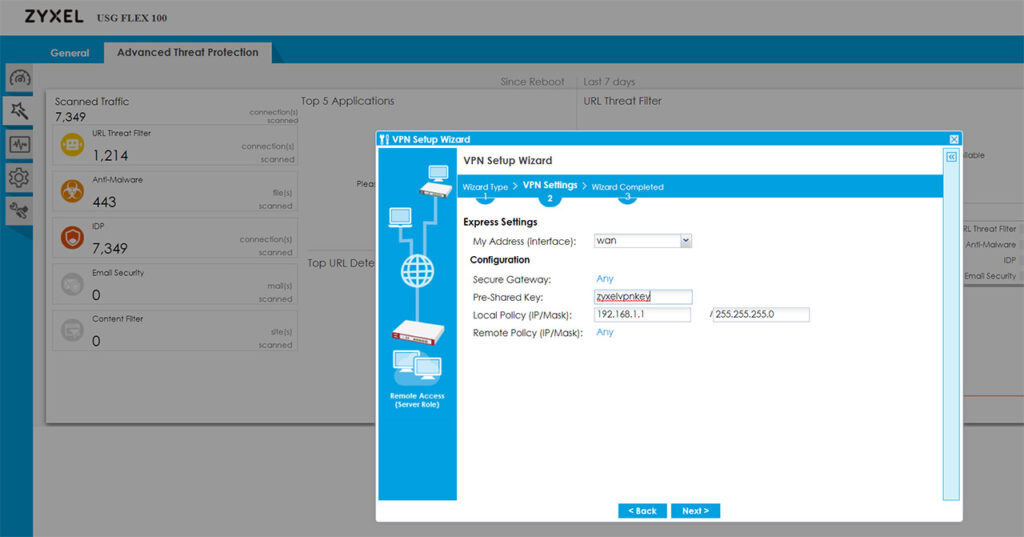
Zyxel has also added guides for the SSL and L2TP VPN configuration and I noticed that there is no Wizard for the SSL VPN. That being said, the process of setting up any VPNs is not really easy, but it’s made a lot more intuitive by the way the interface is designed and especially due to the dedicated walkthroughs for each type of configuration.
Security Features
Some of the most important security features are the Stateful Packet Inspection firewall and you can check the security policies by going to Configuration > Security Policy > Policy Control; here, you can also visit the Anomaly Detection and Prevention (ADP) and add policies for the traffic source and you can also create new ADP profiles (this can be done from the Profile section and you will be able to set the Sensitivity level, the block period for the scan detection, as well as for the Flood Detection). Under the Security Service, you can create App Patrol profiles which will allow the prioritization of certain app over others, as well as the possibility to block or throttle some services based on category or name (this feature does rely on Deep Packet Inspection to get a higher degree of precision).
The Content Filter is another important feature of any Unified Threat Management appliance which allows the user to set rules for the type of content that’s allowed or should be blocked (there is a very extensive list of categories, but you can also add Custom Services) and then, there’s the Anti-Malware, where you can set which type of files to scan, the mode, create a Block/White list and more.
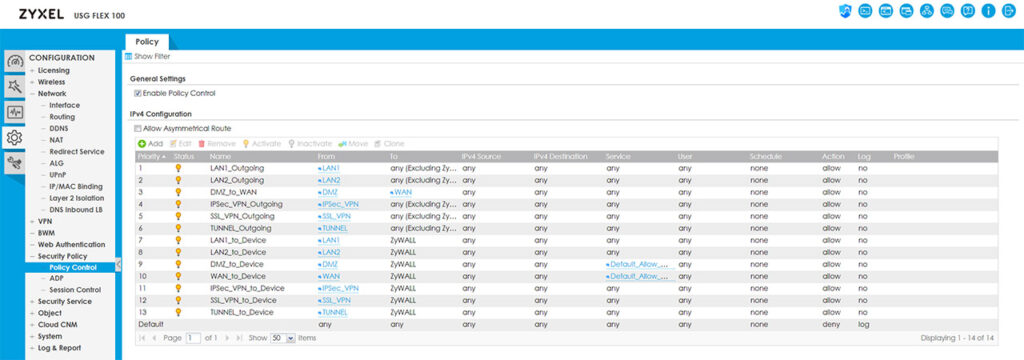
You can also block or allow certain types of URLs under the Reputation Filter, enable IDP (it does require a license) which is an extremely important feature for a security gateway due to its ability to detect any threats from malicious third-parties (viruses, hacking attempts and so on) but be aware that it does have an impact on the throughput, as I saw an average of 500 Mbps (from a Gigabit connection) when the IDP was enabled.
It’s also worth mentioning the Email Security (great at detecting Spam emails), the SSL Inspection (extremely useful at detecting attacks that try to get through the encrypted traffic which would otherwise bypass the normal defenses) and the IP Inspection (you can set exceptions for certain IP addresses, so they’re not affected by the Anti-Malware, UTF or IDP). Besides these security features, you can also access the SecuReporter dashboard by clicking on its dedicated link from the top right corner and doing so, will take you to the Cloud server where you can see any detected malware or blocked requests, as well as a Threat Trend (by levels of potential damage); some additional data can be seen under Analyzer (such as an ADP graph, the Top Threat Website Categories, the Blocked Applications and more).
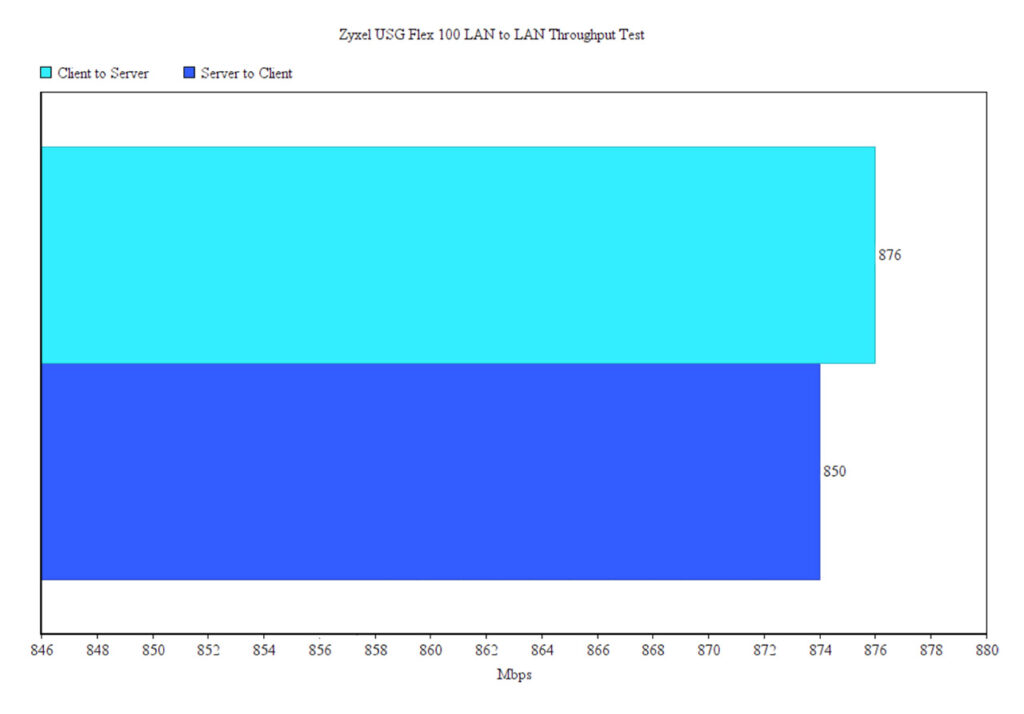
Lastly I decided to run a LAN to LAN test by connecting two computers via Ethernet cables (both devices have Windows 10 OS installed – 64-bit and both had the firewall disabled). This way, I saw an average of 876 Mbps from the client to the server and an average of 850 Mbps from the server to the client which is in line with the 900 Mbps advertised by Zyxel.
Conclusion
Considering that Zyxel has been one of the main suppliers of reliable multi-WAN security gateways for small and medium businesses for more than a decade, there are some high expectations to be met and, after running the USG Flex 100 for a few days, it does seem like the new series does tick all the boxes, especially in terms of security. You get a huge amount of control over what’s blocked and what’s allowed, there are wizards and walkthroughs to help you with any complicated configuration (including steps to set up the IPSec, SSL and L2TP VPNs) and you can balance the load between more than a single WAN port. The internal hardware has also been upgraded to handle more demanding applications without cutting too much from the throughput and the license flexibility is pretty much one of the highlighted features of this new USG series. That being said, similarly to other devices from the USG series, the Zyxel USG Flex 100 supports a huge amount of configurations and the user can adjust pretty much every aspect of their network and while that’s a plus, it can be intimidating for any newcomers. Thankfully, Zyxel has made sure that you are covered for almost any type of application that you’re trying to run, so don’t hesitate consulting the available user manuals and walkthroughs.

[…] Full review […]